


Cyberspace is feeling the strain of Russia’s deadly invasion of Ukraine: multiple sites tied to the Kremlin and its allies in Belarus have been unavailable to all or at least major parts of the Internet in recent days.
The outages began last week with the defacement of Russian websites and picked up steam over the weekend, following a call from Ukraine’s vice prime minister for the formation of an “IT Army” to target Russian interests.
A call to arms
“There will be tasks for everyone,” Vice Prime Minister Mykhailo Fedorov wrote. “We continue to fight on the cyber front. The first task is on the channel for cyber specialists.”
We are creating an IT army. We need digital talents. All operational tasks will be given here: https://t.co/Ie4ESfxoSn. There will be tasks for everyone. We continue to fight on the cyber front. The first task is on the channel for cyber specialists.
— Mykhailo Fedorov (@FedorovMykhailo) February 26, 2022
The task list included 31 organizations affiliated with the Kremlin, Russian banks and corporations, and Belarus. Targets also include Russian government agencies, government IP addresses, government storage devices and mail servers, and support for critical infrastructure. For a time, the popular Russian search engine and email portal, Yandex, was also rendered unavailable.
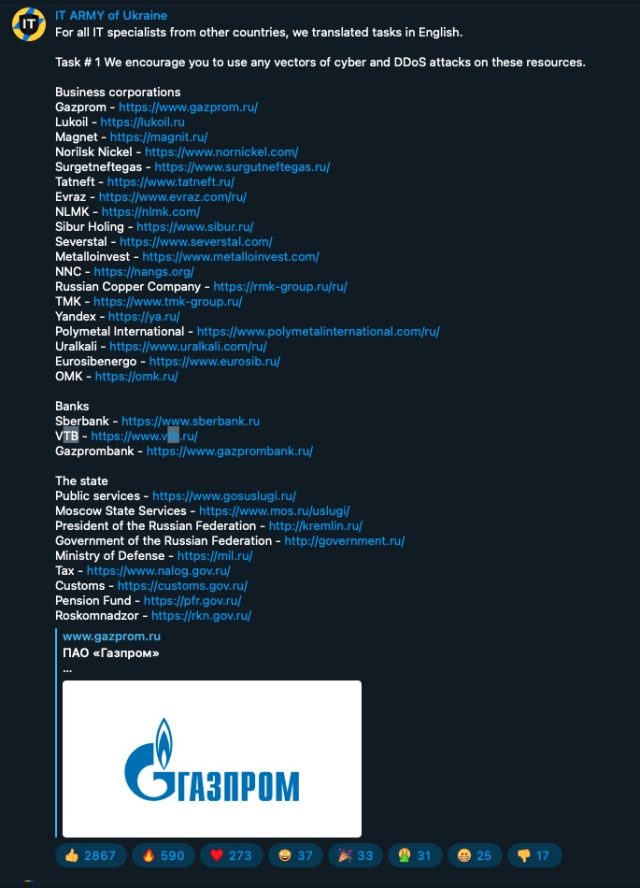
Websites for many of the listed organizations—including banks (Gazprombank), companies (Sberbank), corporations (Russian Copper Company and Lukoil), and government websites (Moscow State Services and the Ministry of Defense)—were unavailable at the time this post went live.
The Cyberpolice of Ukraine, meanwhile, reported on Sunday that IT working on behalf of the country had successfully blocked web surfers from reaching a host of high-profile Russian sites.
Currently down
“Cyber specialists carry out massive cyber attacks on the web resources of Russia and Belarus,” the post stated. “The website of the Investigative Committee of the Russian Federation, the FSB of the Russian Federation, Sberbank, and other important government and critical information systems for the Russian Federation and Belarus are currently down.”
The post said that the sites taken down included the following, all of which were unreachable at the time this post went live:
- sberbank.ru
- vsrf.ru
- scrf.gov.ru
- kremlin.ru
- radiobelarus.by
- rec.gov.by
- sb.by
- belarus.by
- belta.by
- tvr.by
On Monday, Internet traffic from outside of Russia was completely blocked from accessing the site for Russia’s e-government portal. As noted by Doug Madory, director of Internet analysis for network analytics company Kentik, Russia’s biggest Internet provider, Rostelecom, stopped announcing the BGP routes for the portal to contain a nonstop barrage of junk traffic that had been flooding it.
As a result, the site was unavailable to everyone using IP addresses assigned outside of Russia. Exceptions include Microsoft’s Azure points-of-presence.
“This site is probably mostly used domestically, so it probably isn’t a big deal that outsiders can’t access it,” Madory said in a chat. “However, it is evidence that RU is taking defensive measures against attacks on government sites.”
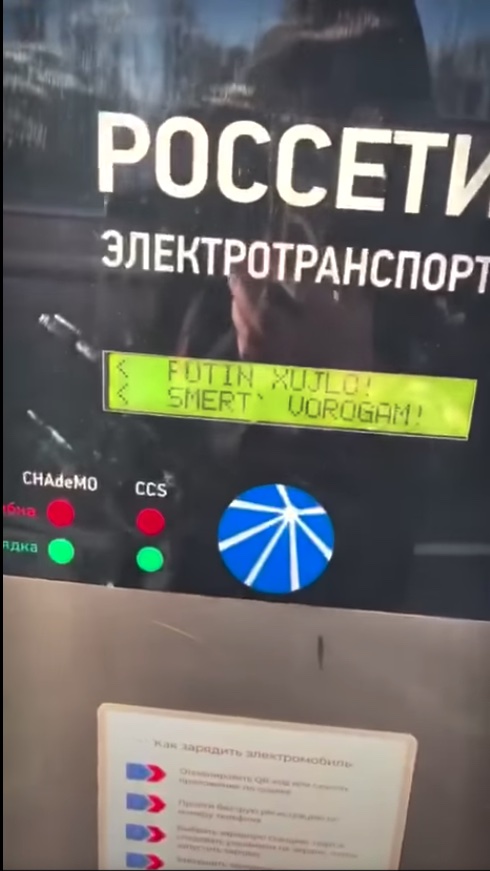
According to a Facebook post published by Russian energy company Rosseti, electric vehicle charging stations in Russia stopped working when the Ukrainian company that provided parts for the stations hacked them by using a backdoor in the charger control systems. Instead of recharging vehicles, the stations displayed a message that said, among other things: “GLORY TO UKRAINE / GLORY TO THE HEROES / PUTIN IS A DICKHEAD / DEATH TO THE ENEMY.”
While much of the attention has focused on Ukraine’s use of DDoS attacks to disrupt or outright block Russian sites, the smaller nation has also been on the receiving end of malicious hacking as well. Last week, researchers from security firm ESET said its researchers discovered never-before seen data wiper malware installed on hundreds of computers in Ukraine.
Breaking. #ESETResearch discovered a new data wiper malware used in Ukraine today. ESET telemetry shows that it was installed on hundreds of machines in the country. This follows the DDoS attacks against several Ukrainian websites earlier today 1/n
— ESET research (@ESETresearch) February 23, 2022
Researchers from Symantec soon confirmed the findings. They, too, had found malware targeting banks and organizations in Ukraine’s defense, aviation, and IT services industries.
A technical analysis from Juan Andrés Guerrero-Saade, principal threat researcher at SentinelOne, said HermeticWiper, as the new malware has been named, follows a “tried and tested technique” of abusing a benign partition management driver to permanently destroy data stored on hard drives.
Two previous wipers—Destover from North Korea’s Lazarus Group and Shamoon from a group known as APT33—abused the Eldos Rawdisk driver to get direct userland access to the filesystem without calling Windows APIs. Guerrero-Saade said that HermeticWiper uses a similar technique by abusing a different driver, empntdrv.sys.
Last week, security researchers said that Russia’s most cutthroat hacking group had deployed new malware for infecting network devices so they could be used to steal passwords and other sensitive data or as a proxy for concealing cyberattacks on other organizations. Ukrainian websites have also been made unreachable in DDoS attacks.
Hackers working on behalf of the Russian government have been behind highly destructive attacks in the past, with the best known being the NotPetya wiper attacks that caused $10 billion in losses for companies all over the world. Russian hackers have also shut down Ukraine’s power grid not just once but twice.
