



Getty Images
Orange España, Spain’s second-biggest mobile operator, suffered a major outage on Wednesday after an unknown party obtained a “ridiculously weak” password and used it to access an account for managing the global routing table that controls which networks deliver the company’s Internet traffic, researchers said.
The hijacking began around 9:28 Coordinated Universal Time (about 2:28 Pacific time) when the party logged into Orange’s RIPE NCC account using the password “ripeadmin” (minus the quotation marks). The RIPE Network Coordination Center is one of five Regional Internet Registries, which are responsible for managing and allocating IP addresses to Internet service providers, telecommunication organizations, and companies that manage their own network infrastructure. RIPE serves 75 countries in Europe, the Middle East, and Central Asia.
“Things got ugly”
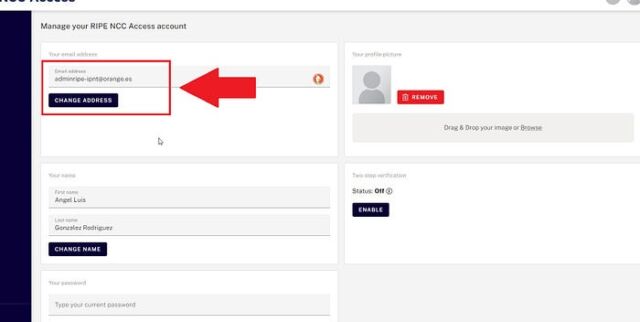
The password came to light after the party, using the moniker Snow, posted an image to social media that showed the orange.es email address associated with the RIPE account. RIPE said it’s working on ways to beef up account security.
Security firm Hudson Rock plugged the email address into a database it maintains to track credentials for sale in online bazaars. In a post, the security firm said the username and “ridiculously weak” password were harvested by information-stealing malware that had been installed on an Orange computer since September. The password was then made available for sale on an infostealer marketplace.
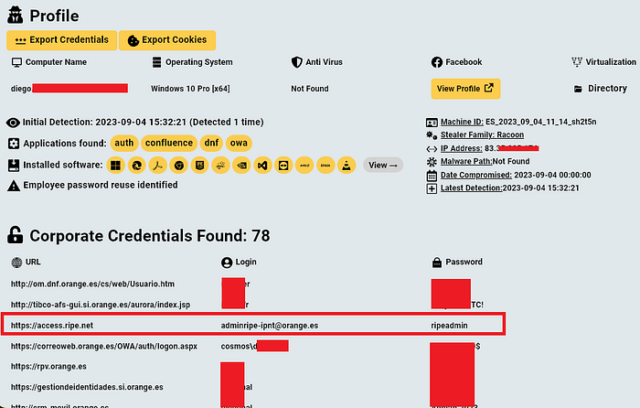
HJudson Rock
Researcher Kevin Beaumont said thousands of credentials protecting other RIPE accounts are also available in such marketplaces.
Once logged into Orange’s RIPE account, Snow made changes to the global routing table the mobile operator relies on to specify what backbone providers are authorized to carry its traffic to various parts of the world. These tables are managed using the Border Gateway Protocol (BGP), which connects one regional network to the rest of the Internet. Specifically, Snow added several new ROAs, short for Route Origin Authorizations. These entries allow “autonomous systems” such as Orange’s AS12479 to designate other autonomous systems or large chunks of IP addresses to deliver its traffic to various regions of the world.
In the initial stage, the changes had no meaningful effect because the ROAs Snow added announcing the IP addresses—93.117.88.0/22 and 93.117.88.0/21, and 149.74.0.0/16—already originated with Orange’s AS12479. A few minutes later, Snow added ROAs to five additional routes. All but one of them also originated with the Orange AS, and once again had no effect on traffic, according to a detailed writeup of the event by Doug Madory, a BGP expert at security and networking firm Kentik.
The creation of the ROA for 149.74.0.0/16 was the first act by Snow to create problems, because the maximum prefix length was set to 16, rendering any smaller routes using the address range invalid
“It invalidated any routes that are more specific (longer prefix length) than a 16,” Madory told Ars in an online interview. “So routes like 149.74.100.0/23 became invalid and started getting filtered. Then [Snow] created more ROAs to cover those routes. Why? Not sure. I think, at first, they were just messing around. Before that ROA was created, there was no ROA to assert anything about this address range.”
